The internet has come a long way from its humble debut many years ago. From days when the only occupants were HTML files that required store-sized compartments to move around to the Web3 age where you can spend your entire day immersed in a plethora of dynamic online pleasures. In all that growth, one need has remained paramount and without compromise – cybersecurity. In this article, we will delve into the cybersecurity essentials and how it affects you as a small and middle-sized business owner. Let’s get right in.
Overview of some Cybersecurity Essentials and Why It Is important For SMBs

Cybersecurity, as the term implies, is simply the protection of sensitive information. It is the technology that is put in place to protect a system’s network and devices from damage, attack, and even unauthorized data access. If you own a mobile device and currently use a password, you’ve successfully implemented a cyber security measure, however simple.
How does this matter to you as a small or medium-sized business owner?
Our mobile devices are compact working systems that contain sensitive data about our personal lives. How much more sensitive information about our businesses? There’s a cognitive bias that cybercriminals are mostly interested in the Apple Inc. of this world. If only that were true, this article would be addressed to larger corporations. Unfortunately, that is not the whole story. The sentiment is completely understandable, partly because larger corporations have the most to lose and also because they’re the ones making the headlines.
There’s a sad truth to why SMBs should pay serious attention to the security of their business. Small to mid-size businesses often lack effective cybersecurity strategies and systems due to insufficient funds to develop and implement them. Some SMB owners are often ignorant about the advantages of good cyber security practices or unwilling to implement them because they believe their business is under the radar of cyber threats. All of these have led to an increasing number of attacks on SMBs.
Understanding the Basic Concept of Cybersecurity
Understanding the basics of cyber security concepts is only the first step in protecting your business from cyber-attacks. The core principles of cybersecurity generally encompass the computer procedures and methods formulated and executed to protect systems, network servers, and software applications from unauthorized digital breaches.
Why Cyber Security is Fundamental for Business Success
The heartbeat of business success resonates with the vital rhythm of cybersecurity. Just as a fortress shields a kingdom from threats, cybersecurity stands as the guardian of modern enterprises. Still don’t think cybersecurity is important to saving you money or ensuring smooth business operations? Here’s something to chew on: According to Security Intelligence, losses from cyberattacks were estimated to be over $10 Billion – that’s more than most small businesses make in their lifetime. Cybersecurity threats pose a serious deterrent to the success of any business; therefore, a business owner must strive to understand the fundamentals of cybersecurity.
Common Cyber Threats Faced By SMBs
There are quite a number of ways hackers can gain access to a business. The more common types of attacks include
Phishing Attacks: Phishing involves the sneaky tactic of getting people to share personal info or click on bad links through fake emails or messages. In small and medium businesses (SMBs), workers might unknowingly spill the beans on login details or financial info, which could lead to big data leaks or money problems.
Ransomware: This nasty type of software locks up a company’s data and demands a payoff to unlock it. SMBs often end up in the crosshairs because they don’t have tons of cybersecurity backups, making them more likely to cough up the cash.
Malware, like viruses, worms, and Trojan horses, is the bad stuff that can infect computers, swipe data, or make life difficult. If employees at SMBs click on fishy links or iffy attachments, they’re essentially rolling out the welcome mat for malware without even knowing it.
Weak Passwords: Probably the most common issue faced by SMBs on the list. Many business owners have a habit of using flimsy passwords. Worse yet, some recycle passwords and keep the same password for a long time, all of which are unhealthy security habits hackers can take advantage of to disrupt your business.
Data Security and Sensitive Data Protection Practices
When it comes to keeping your data safe and guarding sensitive info, a few practices can make a world of difference:
- Encryption: Think of encryption as turning your data into secret code. This makes it pretty much useless to anyone who shouldn’t be looking at it. Whether it’s emails or files, encrypting them adds an extra layer of protection.
- Access Control: Not everyone in your business needs access to everything. Limiting who can see what data can prevent accidental leaks or intentional snooping.
- Regular Updates: Those software updates you see popping up on your devices? They often include patches that fix security holes. Ignoring them can leave you vulnerable.
- Strong Passwords: Yup, we’re still on this one. A strong password that’s not a cakewalk to guess can save you a lot of trouble.
- Employee Training: You might be surprised at how many data breaches happen due to human error. Educating your team about phishing, safe browsing, and other risks can go a long way.
- Backup, Backup, Backup: It’s like having a spare key hidden somewhere safe. Regularly backing up your data ensures that even if something goes wrong, you’ve got a clean copy to fall back on.
- Physical Security: Don’t forget that data isn’t just digital. Locking up servers and keeping sensitive documents out of sight can prevent physical breaches.
- Monitoring and Detection: Sometimes bad things happen, even with all precautions. Having security tools in place to detect unusual activity can help you catch problems early.
- Clear Policies: Lay down the law when it comes to data security. Ensure your employees know the do’s and don’ts and the consequences of not following them.
- Third-party Vendors: If you’re sharing data with outside companies, ensure they’re as committed to data security as you are. A chain is only as strong as its weakest link, after all.
Essential Security Measures to Implement in SMBs

Let’s discuss some super important security steps that Small and Medium-sized Businesses (SMBs) should think about implementing:
Firewalls: Imagine firewalls as your protective shield online. They create a force field between your internal network and all the potential trouble out there. Basically, they sift out the bad stuff and keep the good stuff safe.
Antivirus and Antimalware Software: These are like the bodyguards for your devices. You want them installed on all your gadgets. They’re really good at spotting and kicking out any sneaky software that could mess things up.
Regular Software Updates: Updates are like patches you make for your digital clothes. They keep things from getting worn out and shabby. By keeping everything up to date, you’re actually closing the doors on any sneaky hackers trying to slip in through known gaps.
Strong Password Policies: You know those complicated, mix-and-match passwords? Those are like your secret code to protect your digital treasures. Get everyone on your team to use them, and you’ll be locking the virtual doors tight.
Multi-Factor Authentication (MFA): This is like having not just one but two or more locks on your digital safe. Even if someone gets hold of your password, they still need another secret handshake to get in.
Understanding the CIA Triad in Cybersecurity
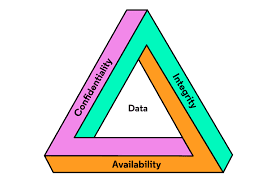
Not to be mistaken for the world’s most popular intelligence department, the CIA triad is a model in cybersecurity that shields your digital space from an attacker. Think of it as core life principles we all have that guide how we do things but for a business’s online security.
What is the CIA Triad in Cybersecurity?
The CIA acronym in cybersecurity stands for three things:
- Confidentiality: One of the first rules in storing valuable information is keeping a secret. Only the right people should get access to sensitive info. Much like a lock you place on a diary – you wouldn’t want just anyone reading your secrets. Things like encryption and special permissions make sure only the right folks can see the important stuff.
- Integrity: This is all about making sure your information doesn’t get messed with. Imagine you have a book report – you want to ensure nobody sneaks in and changes your words, right? Data integrity is like a digital lock that prevents unauthorized changes. It ensures your data stays accurate and trustworthy.
- Availability: This is like making sure your favorite game is always ready to play. You want your stuff to be there when you need it. Availability means your digital tools and data are always up and running, without any hiccups. Backups and plans for when things go wrong help keep everything available.
The Importance of Confidentiality in the CIA Triad
Confidentiality is the Batman of the CIA Triad in cybersecurity. It’s all about keeping your secret stuff really, well, secret. Making sure only the right people can peek at your private things. When we lock down confidentiality, we stop unauthorized folks from getting their hands on important data. Cool tricks like encryption and strict access rules make sure your info stays safe from nosy people and potential security breaches.
Digging Into the Concept of Integrity
Let’s dive into what integrity means in the CIA Triad of cybersecurity. It’s all about ensuring that your data stays true and unchanged, just like you intended it to be. It acts as a digital watchdog that barks if someone tries to mess with your information. By focusing on integrity, we make sure that only the right changes happen to your data, and that unauthorized alterations are stopped in their tracks.
Understanding Availability as a Key to Cybersecurity
Availability as a cybersecurity concept is what makes the entire cybersecurity operation accessible and useful. After you’re done setting up your security strategy, it makes no sense if those strategies can’t be called upon when there’s a threat lurking around.
How the CIA Triad Protects Against Cyber Attacks
We’ve taken each triad and explored how they act individually to protect your business. Together, these three elements make for a bulletproof vest that defends and protects your organization from even the most determined hacker.
Demystifying Common Types of Cyber Attacks and Their Impact
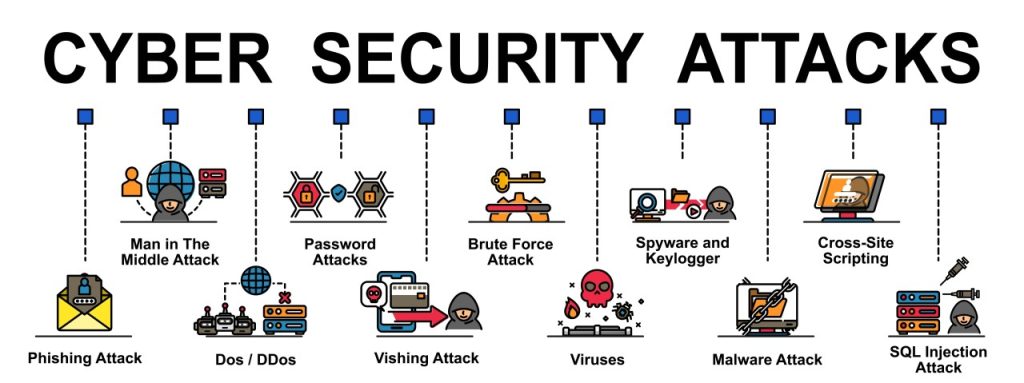
If you’re not well versed in the more technical aspects of cybersecurity, it’s easy to get lost and remain ignorant of the threats cyber attacks pose to you, individually and as a business.
Understanding Different Types of Cyber Attacks
Generally, in our daily lives, simple is often the most effective in accomplishing any task. This sentiment also applies to cybercriminals and their methods, and you’d be surprised how simple it can be to hack into a business’s security system. Examples are Password breaches, malware like viruses or ransomware, phishing links, etc.
How Malware and Malicious Code Threaten SMBs
Small and Medium-sized Businesses (SMBs) are at risk when it comes to cyber threats like malware due to their vulnerabilities. With limited resources and not having dedicated cybersecurity experts, they become attractive targets. To stay safe, SMBs need to educate their team through training programs, understand different types of malware, and put strong cybersecurity measures in place.
Social Engineering Attacks and Their Consequences
Social engineering attacks are on a swift rise, especially in sophistication. In the past year, we’ve seen how devastating they can be to the people involved. Reports suggest that more than 95% of cyberattacks rely on social engineering to be successful! So, what does a successful social-engineered cyber attack look like? Social engineering could lead to identity theft, ransomware attacks, damage to one’s reputation, unauthorized access, etc.
The Risks and Impacts of Data Breaches
Imagine a cybercriminal gains access to your account details or credit card numbers in a data breach; they could make off with a life’s worth of investment, savings, capital, or profit. What would that do to you as an individual and to your business at any scale? A lot of damage. It doesn’t just end in financial loss; data breaches could effectively shut down business operations and make a huge dent in your reputation as a business, causing you to lose clients or customers.
Cybersecurity Protocols to Counter These Attacks
Having a robust security solution is essential to protecting your business. Here are some security fundamentals that can help you prevent attacks:
Hire Cybersecurity Professionals: We get it; running a business and being a security expert isn’t your cup of tea. That’s exactly why getting an expert is a great idea. They not only save you the hassle of setting up a security architecture by yourself, but they also save you future curative expenses in case of a successful attack.
Keep your software and systems up to date: The importance of software updates can’t be hammered on enough. Update the system as often as required. Updates usually contain new patches to help deal with malware and other forms of cyber attacks.
Endpoint Security: You probably haven’t heard of this one. Endpoint protection simply means protecting networks that are remotely bridged by devices. A typical example of such a network is mobile devices used by remote employees.
Backup your data: You did all you could, but life happened, and your business came under fire from cyber criminals; having a backup to restore after the ordeal will be something to appreciate.
Exploring Job Roles and Career Opportunities in Cybersecurity

What if you were told that the average salary in the cybersecurity field is anywhere from $70,000 to $90,000? Pretty decent, right? Let’s explore roles and career opportunities in cyber security.
Security Engineer: A Key Cybersecurity Role
In our digital world, Security Engineers are the unsung heroes who keep our sensitive info safe from all those sneaky cyber threats. They’re the ones setting up strong defences, finding weak spots, and tackling emergencies to make sure our online space stays secure. Better yet, a security engineer is among the most sought-after professionals in the industry, and many companies will pay top dollar to get one on their team.
Paving the Way for a Career in Cybersecurity
Thinking about diving into the world of cybersecurity? Smart move!
From getting an education to grabbing those certifications and hands-on experience, there are loads of ways to kickstart a cool career in this ever-growing field.
CompTIA Security: A Valuable Step in a Cybersecurity Career
If you’re gearing up for a cybersecurity adventure, CompTIA Security+ is a trusty sidekick. It lays down the basics, helps you understand the tricks and threats, and boosts your chances of landing a top-notch gig in the cybersecurity world. CompTIA Security+ is a globally recognized certificate that validates its holder as having the necessary skills to perform fundamental security functions and also pursues a cybersecurity career.
Skill Sets Required for a Successful Cybersecurity Career
Cybersecurity champs aren’t just tech wizards – they’re also savvy problem solvers and smooth talkers. They need to have the necessary knowledge and skills to find their way around network security and encryption while staying on top of the latest bad-guy tactics. Here are 7 must-haves for a successful cybersecurity career:
- Fundamental technological skills: Don’t fret; just being moderately tech-savvy is the goal here. It’s alright if you can’t build a spaceship.
- Programming: You can’t fight codes if you can’t write codes.
- Communication skills: You have to be able to articulate information to be a successful IT guy.
- Risk identification and management.
- Data management and analysis.
- Cloud implementation and management.
- Logical reasoning and troubleshooting.
Potential Opportunities and Career Paths in Cybersecurity
Picture a world where you can play the digital hero in various ways: from spotting vulnerabilities as a Security Analyst to calling the shots as a Chief Information Security Officer (CISO). And that’s just the tip of the cybersecurity iceberg!
Unpacking Basic Cybersecurity Terminologies and Best Practices
Want to know how to talk the cybersecurity talk? We’ve got you covered with the basics. Malware, encryption, and all that tech jazz – we’ll break it down so you can stay smart online.
Common Cybersecurity Terminologies: A Beginner’s Guide
Some basic terminologies you should know;
- Authentication: The process of confirming the identity of someone who wants to access sensitive data.
- BotNet: A nice catchy term for robot and network. Typically, it refers to a computer system that has been infected by viruses and is constantly working to create data breaches.
- Data Breach: This one has come up a few times in the article. It means that a hacker has successfully infiltrated a system and now has access to sensitive data like bank account details, etc.
- DDoS: Stands for Distributed Denial of Service, which is just a fancy phrase that means hackers have bombarded a system with a rush of requests and the system shuts down in response.
- Domain: A series of devices working and simultaneously connected as one entity. Think of it as a hydra system of electronic devices.
- Encryption: A series of codes used to protect your data from hackers.
- Malware: Another amalgamation of words, in this case, “malicious” and “software” were mashed up. It means any software that is designed to harm a system.
- Phishing: An elaborate scam where a hacker pretends to be a legitimate organization and individual to fool a victim into revealing sensitive personal info. Hackers can accomplish this by sending fake links or documents containing malware to the unsuspecting victim.
- Ransomware: A kind of malware that literally kidnaps an entire system and holds it for ransom. Clever naming.
- Virus: This is the OG malware and probably the most common term on the list. Like its biological counterpart, a virus is malware that infects a system to corrupt or destroy the data within it.
Importance of Regular Security Updates
Without meandering, we can sum up the major importance of regular security updates as SECURITY! But new updates do have more impact on software than just security.
1. To patch and secure system vulnerabilities: This point can’t be overstated as it is – repeatedly – the most critical part of every new update. Have you ever wondered why security-conscious folks don’t like old computers or mobile phones? Older devices may not be supported by the manufacturer, so they would no longer get security updates.
2. New Features and Improved Usability: New updates come with new features to improve the entire user experience of the device.
3. Ensure Compatibility: Here’s another super important reason for updates; as your devices age, new software and applications will no longer work on them. Security updates come with patches to help improve the device’s lifespan, almost like an anti-aging potion, but not quite.
Effective Security Policies For SMBs
As a business owner, you’re most definitely the ruler of your empire, and your security team are your councilors or cabinet. It would be wise to listen to them, and together, you can formulate effective policies to protect your business empire. Some of those policies can be:
- Physical Security
- Password Policy
- Internet Use Policy
- Email Use Policy
- Corporate Devices Policy
- Personal Devices Policy
- Data Security and Transfer Guidelines
- Training Requirements
Best Practices While Connecting to the Internet
We all want free Wi-Fi sometimes, don’t we? But not all accessible Wi-Fi networks are what they appear to be.
- Password Power: Make sure everyone follows the rule of crafting passwords that are tough to guess.
- Access Control: Since we’re on the matter of your empire, imagine having different levels of access badges in your empire – not everyone gets access to the high-security areas. Apply this concept to your business’s data: restrict access to sensitive information only to those who need it.
- Employee Education: Just like citizens need to know how to spot potential dangers, your employees should be aware of digital threats. Educate them about phishing emails, malicious links, and the importance of cybersecurity hygiene.
- Regular Updates: You’d regularly fix broken streetlights and potholes in a bustling city. Similarly, make sure all your software and systems are up to date. These updates often patch up vulnerabilities that hackers could exploit.
- Secure Devices: Think of your employees’ devices as personal vehicles in your digital city. Ensure they’re equipped with security tools like antivirus software and encrypted connections, just as you’d ensure vehicles have seatbelts and airbags.
- Incident Response: In case of a security breach, you need a plan of action, like having a fire department ready to handle emergencies. A well-defined incident response strategy ensures you can act swiftly to minimize damage.
- Backup Strategy: Imagine if essential documents in your city could disappear – that’d be a nightmare. Similarly, back up your digital data regularly.
- Third-party Vendors: If you allow other businesses into your city, you must ensure they follow the rules. Apply this to your digital space – ensure third-party vendors. adhere to your security standards.
Physical Security: Often Overlooked Aspect of Cybersecurity
In the genius of having cyberspace, it is easy to forget that the components that run this space are primarily physical. If so, taking physical security measures to protect them from harm makes sense. Ensure that only authorized parties can access the physical space where your business devices are stored. Putting a torch to your computers is as effective as damaging your business as malware in your system software.
