
The Dangers of Running Outdated Software
Your software is only as good as its last patch. Reaching End of Life (EoL) or End of Service (EoS) means critical patches and updates

Your software is only as good as its last patch. Reaching End of Life (EoL) or End of Service (EoS) means critical patches and updates

When a software or hardware product reaches its End of Life (EoL) or End of Service (EoS), it’s no longer supported by the manufacturer. This

It’s crucial to keep all software and hardware up to date to maintain optimal security. If you don’t, cybercriminals can easily infiltrate your network and
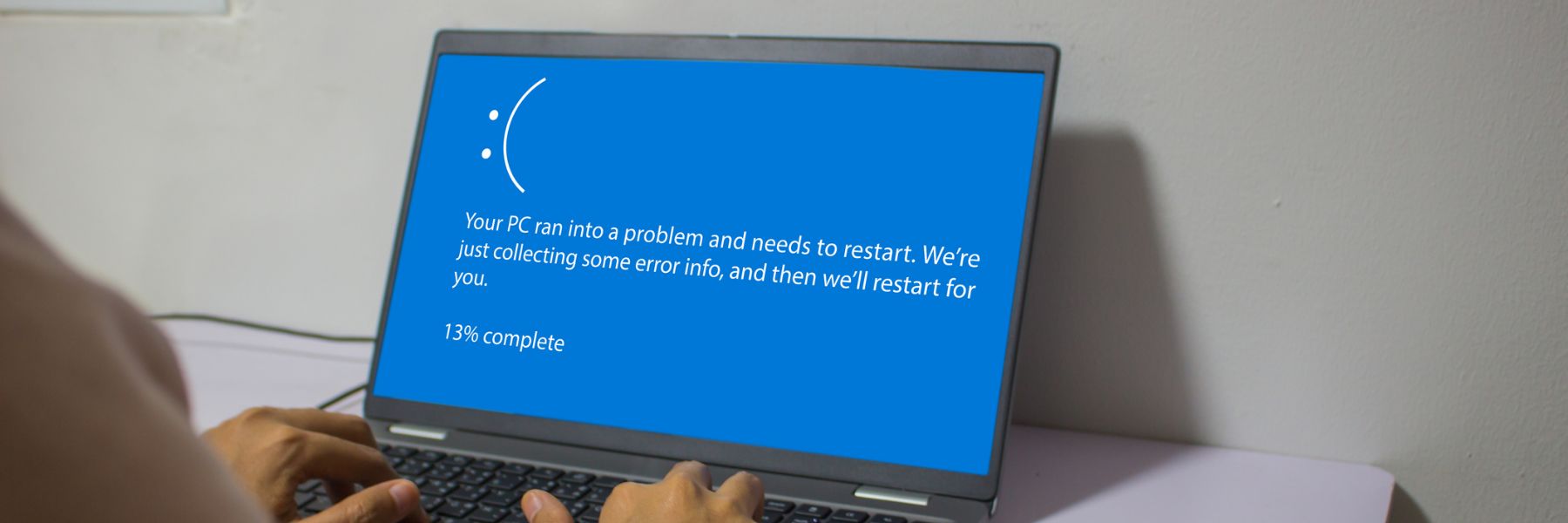
We are all aware of the term “use by date.” It is regularly used when talking about food and medications and refers to the date

In 2021, organizations that didn’t have zero trust incurred an average breach cost of USD 1.76 million more than those organizations with a mature zero-trust

Rapid technological advancement and rising global connectivity are reshaping the way the world is functioning. From higher productivity to improved customer satisfaction, technology has played

Ransomware is a type of malicious software that encrypts files on a device or network, making them unusable until the victim pays the attacker a

In today’s digital age, ransomware attacks are becoming increasingly frequent, sophisticated and costly. With cybercriminals constantly evolving their tactics and targeting businesses of all sizes,

With most companies embracing remote or hybrid workforce models in the wake of the pandemic, cybersecurity threats have grown rapidly across the world. Insider risk

Defense Strategies to Combat Insider Threats Insider threats are among the most dangerous cyberthreats out there. Yet, organizations of all sizes seem to be either