In this article, we’ll be covering everything you need to know about cybersecurity inside-out for your business.
We’ve been in IT since about 1995. Back when everything was completely different.
Today, you have a whole new range of security issues, different pieces, and different risk assessments to consider.
That’s also because cybersecurity is an incredibly wide field.
For small businesses, it’s all about:
- What do your day-to-day operations look like?
- What kind of equipment are you running?
- What kind of scans are you running?
- Are you doing service password resets, two-factor authentication, dark web scans, and so on?
Because this is far from a “once-and-done” thing, it’s easy for small businesses to get overwhelmed when talking about cybersecurity – especially with their limited budget and resources.
Fortunately though, by the end of this article, you’ll have a much better understanding of how to navigate through the cybersecurity spaces as a small business.
Including some obvious cybersecurity best practices and tips that don’t cost a fortune to instill within your small business.
And where to go
Here’s what you’ll learn:
- What is cybersecurity and what small businesses need to know
- Our proven approach to cybersecurity for small businesses: being proactive vs reactive
- Navigating through growing concerns and challenges within the cybersecurity field

What Is Cybersecurity And Why Does It Matter For Small Businesses?
First off, defining what cybersecurity means can be hard.
If you ask 10 small business owners what it means, you’ll get 10 different answers.
That’s because cybersecurity is the culmination of many different things that are always evolving.
Including network security, data protection, vulnerability management, cloud security, and so much more.
So, at its core, no small business is immune to cyber risks because of this.
However, there are certain proactive steps you can take to defend yourself from any potential cybersecurity threats.
Our own approach at MIS Tech is proactive. Which means that prevention is usually better than cure. And we’ll cover this in more detail below.
What small businesses need to know about cybersecurity
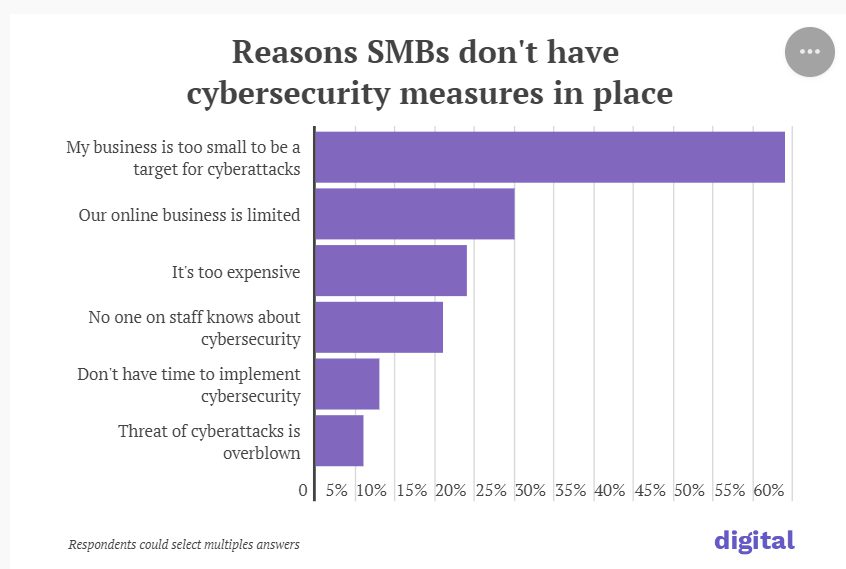
According to a report by Digital, around 51% of small businesses admit to leaving customer data unsecure. And 6 in 10 SMBs think they’re “too small to be a cybersecurity target“.
That belief, however, is often a misconception.
Companies of all size should take cybersecurity seriously. Customer data is always valuable and bad actors may go out of their way to target SMBs because they have less budget for protecting customer information and are therefore easier targets.
This means the following assets could be at potential risk:
- Access to customers list.
- Customer or company credit card information.
- Banking details.
- Pricing structure.
- Contact and personal details.
- Product designs or trade secrets.
- Business plans.
- Other types of intellectual property.
- And more.
Which is why it’s hard to put a cost on cybersecurity breaches.
That said, according to Kaspersky, small and medium businesses lose about $15,000 to $120,000 per cyber incident on average.
Not to mention the recovery cost or indirect costs (such as reputation loss, opportunity cost, emergency infrastructure improvements, and so on).
It’s also worth noting that every small business is different.
For companies in the healthcare industry, you also have to take into consideration HIPAA compliance, for example.
In the case of HIPAA violation, healthcare companies can face severe penalties, including a fine of up to $50,000-$100,000 or worse.
So, if you’re not sure where to start, make sure you always cover the best practices and essentials first.
Enforce 2 factor-authentication
Most platforms allow you to enable 2-factor authentication to keep your accounts more secure nowadays.
2FA is another layer of protection you can use to verify who is actually accessing the account and not someone who’s unauthorized.
Make sure you always have this enabled when you can.
By enabling this, even if someone steals your password, they won’t be able to access your account without the authentication code.
A Google study shows that SMS-based authentication can block up to 100% of automated bots and 99% of bulk phishing attacks.
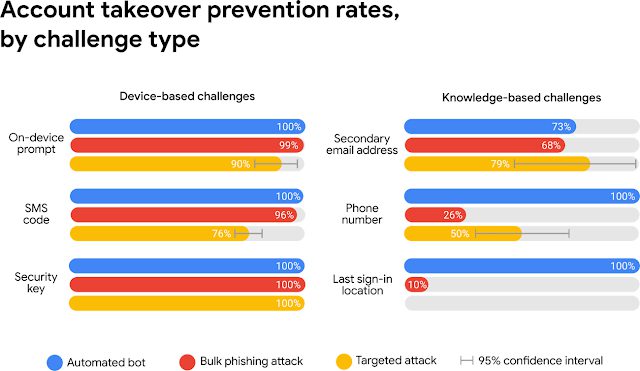
Typically, you receive the authentication code on your mobile (via SMS or an app such as Google Authenticator or Authy).
With MFA (multi-factor authentication), users are required two authentication factors.
Phishing and social engineering
Phishing and social engineering are one of the most common reasons why small businesses get breached.
When it comes to social engineering attacks, an attacker uses human interaction to obtain or compromise information about a company or its systems.
An example of a phishing attack might be as follows:
- You receive an email that appears to be from the bank, informing you of suspicious activity.
- The email contains a link to “verify their account”.
- The link redirects to a fake website that looks identical to the bank’s website. Through which, the hacker obtains login credentials.
Social engineering, meanwhile, attempts to exploit human psychology, trust, and often relies on establishing rapport with a target.
Though avoiding these might seem obvious when you’re reading this, it’s still essential to train your employees and carry out risk assessments to avoid cybersecurity attacks.
Being Proactive VS Reactive When It Comes To Cybersecurity (Our Proven Approach For Small Businesses)
When it comes to cybersecurity, we take more of a proactive stance than a reactive one.
Here’s what this means:
- Being proactive means taking measures and planning ahead to mitigate potential risks and threats before they cause harm.
- Being reactive involves responding to cybersecurity incidents and threats after they have already occurred.
We favor the proactive approach by setting up security elements such as:
- User training – Providing regular cybersecurity training, awareness, and best practices for maintaining secure digital behavior.
- Security measures – Implementing measures such as firewalls, intrusion detection, prevention systems, antivirus, and more.
- Patch management – Ensuring software, operating systems, and applications are up-to-date with the latest security patches to address known vulnerabilities.
- Incident response planning – Developing and practicing incident response plans to handle potential security breaches or cyber incidents.
At MIS Tech, we work with clients as an outsourced IT solution.
And typically, in the past, if someone wanted to reset their password, they would call us on the phone.
However, nowadays, it’s easy through social engineering for a cyber attacker to impersonate someone else.
To prevent this, we’ve started introducing self-service password resets (SSPR) as a way for users to reset or change passwords without requiring assistance from IT support or administrators at all.
Here’s how this works:
- Users enroll in a self-service password reset system initially once.
- Then, if a user forgets their password or needs to change it, they access the self-service password reset portal or link, usually available on the login page.
- The system verifies the user’s identity through a pre-defined security measure. This could involve answering security questions, entering a verification code sent to their registered email or phone, or through an MFA challenge.
- Finally, once the identity is verified, they’re granted access to change or reset their password.
This is just one example, of course.
But the point is, when it comes to cybersecurity, it’s very common to see trends and best practices change.
Which is why it’s also so important to be constantly monitoring and optimizing your systems.
That said, no password is going to be unbreakable.
But this is also why it’s so important to have a proactive, multi-layer cybersecurity approach that covers your firewall, two-factor authentication, employee awareness, and more.
Navigating Through The Cybersecurity Field (Growing Concerns And Challenges)
25 years ago, there was no real cybersecurity path. While now, there are 50+ million unoccupied cybersecurity jobs.
The point here is that as technology advances, so does virtually everything that is related to it.
Including how our lives evolve around IT and cybersecurity.
For example, the growing number of connected devices we use is expanding the potential attack surface.
IoT (Internet of Things) means more smart cameras, TVs, smartphones, speakers, light bulbs, and so many new things. If breached, attackers can gain access from those devices into your system and cause havoc.
As a result, it’s more important than ever to be constantly on top of things.
We’re looking at the latest logs, cybersecurity trends, and even the latest cybersecurity attacks to learn from them and make sure we set up preventive measures.
Dangers of outdated systems and technology
One very common cybersecurity pattern we’ve seen in small businesses has to do with outdated systems and tech.
While inconvenient, maintaining regular software updates is essential for eliminating known vulnerabilities that bad actors exploit.
Prioritize timely patching for you:
- Operating systems.
- Applications and software.
- Network devices.
- And firmware.
Make sure you set automated patches so nothing falls between the cracks.
Any kind of legacy technology you still use comes with huge security risks.
That’s because they no longer receive vital software patches and create gaps in visibility and control.
For example, January 10, 2023 marks the end of Microsoft’s support for Windows 7 and 8.1.
This means they will no longer release security and bug updates. And if your business still uses those, operating systems, hackers are likely to discover new security exploits and target businesses still running those systems.
Conducting periodic technology risk assessments to identify end-of-life systems to upgrade or replace can be a great way to reduce the risk of all this.
What happens to small businesses in the case of a cybersecurity breach
While our approach is that prevention is better than cure, cyber attacks can still happen.
And it’s going to hurt 2 main things:
- Your revenue – A cybersecurity breach disrupts your day-to-day operations, leading to downtime and loss of productivity. This can also directly affect lost sales and missed business opportunities.
- And your reputation – Customers and clients that expect their data to be handled securely and responsibly may lead them to question your business credibility and commitment to safeguarding that info.
Ultimately, the goal is to prevent cybersecurity breaches before they occur.
By maintaining up-to-date systems, implementing robust security measures, and fostering a security-conscious culture among your employees – you can significantly reduce the risk of a breach.
Where To Go From Here
So, where do you go from here?
As a small business, if you want to navigate through the cybersecurity field effectively, you need to:
- Prioritize cybersecurity and adopt a proactive culture.
- Conduct an internal risk assessment.
- Implement strong security controls.
- Educate your employees.
- Stay updated and optimize your cybersecurity regulations over time.
Of course, this is a big generalization. Because cybersecurity is a constantly growing field and simply put, it’s not that simple.
So, if you’re a small business looking for an all-in-one cybersecurity program, join forces with MIS Solutions now with a cybersecurity assessment intro now!
Our meticulous cyber assessments cover all aspects of your cybersecurity:
- Risk assessment.
- Penetration testing.
- Posture assessment.
- Vulnerability assessment.
- Compliance assessment.
- And more, as needed.
Now, to sum up:
- What is the importance of cyber security?
Cybersecurity is important for businesses of all sizes, but especially small ones.
It protects you from cyber threats, safeguards your reputation, ensures business continuity, ensures legal compliance, and finally – protects your financial assets. Sensitive data often includes protected health information (PHI), personally identifiable information (PII), intellectual property (IP), and other form of information.
- How cyber security can protect your business?
Cybersecurity protects your business by implementing different strategies and practices to safeguard your digital assets. Ways cybersecurity protects your business include:
- Data protection.
- Network security.
- Employee awareness.
- Incident response planning.
- Patch management.
- And more.
- What are the three main important areas of cybersecurity?
The three main important areas of cybersecurity include:
- Network security – Protecting the organization’s computer networks from unauthorized access, data breaches, and other cyber threats.
- Data protection – Protecting data from unauthorized breaches, theft, or manipulation by unknown attackers.
- Employee education and awareness – Human error is a significant factor in cybersecurity breaches. Educating employees about risks and best practices is essential for creating a security-conscious culture within the business.
